Introduction
When you hear "hacker trying to guess your password," you probably imagine someone typing frantically on a keyboard.
In reality, hacking is automated math. It is software trying millions of keys per second until the door opens.
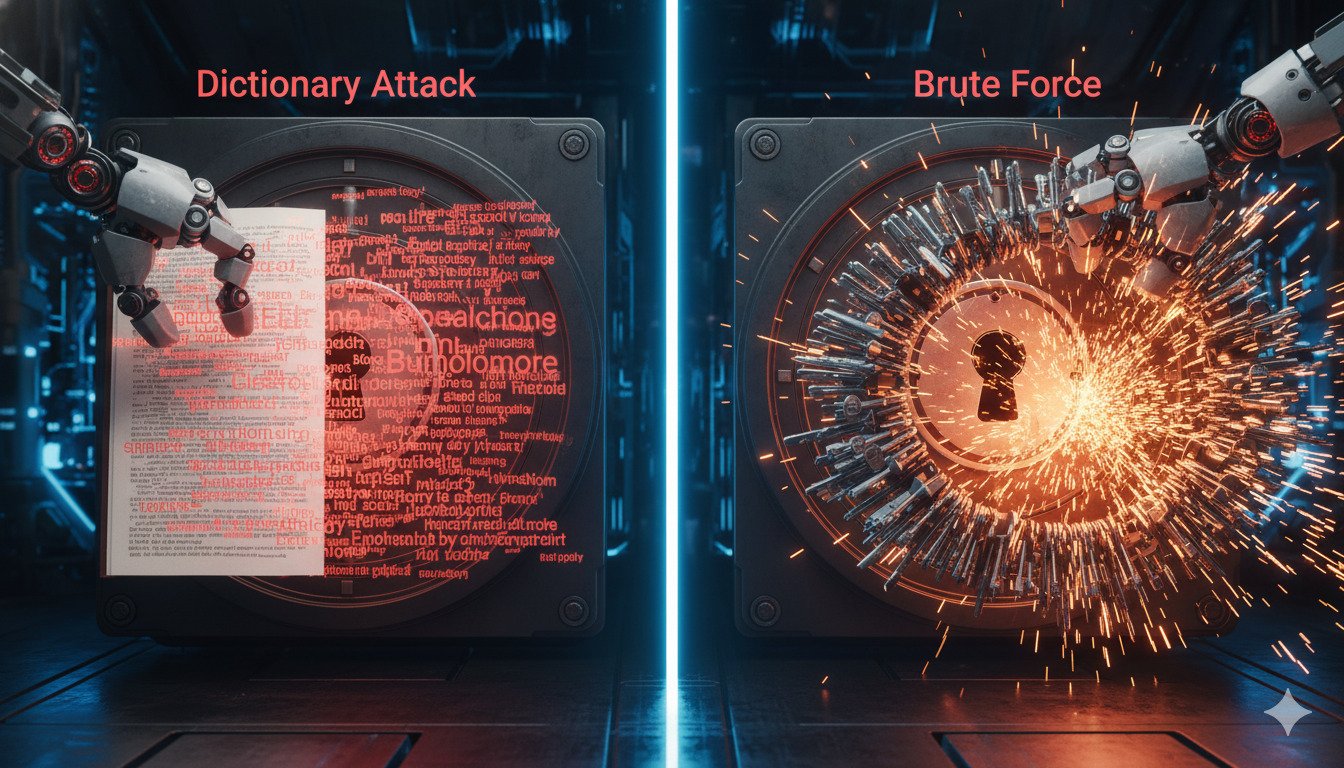
But not all automated attacks are the same. There are two main strategies hackers use: the Brute Force (trying everything) and the Dictionary Attack (trying likely things). Understanding the difference is the key to creating a password that actually works.
The Dumb Hacker vs. The Smart Hacker
Imagine you lost the combination to a 4-digit padlock.
- Method A: You start at 0000, then 0001, 0002, 0003... all the way to 9999. You will eventually open it, but it takes time. This is Brute Force.
- Method B: You think, "Most people use birth years." So you try 1980, 1981... up to 2010. You try only 30 combinations instead of 10,000. This is a Dictionary Attack.
What is a Brute Force Attack?
A Brute Force attack is pure exhaustion. The software tries every possible combination of characters.
aaaaaaaaaaabaaaaac
Strengths: guaranteed to work... eventually. Weaknesses: incredibly slow. As you add length to a password, the time required grows exponentially. Cracking a 12-character password by brute force would take millions of years.
What is a Dictionary Attack?
Hackers know that humans aren't random. We use words. We use names. We use "password."
A Dictionary Attack skips the random gibberish (xk9#m!) and only tries words from a pre-defined list (a "Dictionary").
This list includes:
- Every word in the English language.
- Popular passwords (
123456,password,qwerty). - Pop culture terms (
Superman,StarWars). - Leaked passwords from other breaches.
Strengths: incredibly fast. It can guess millions of "likely" passwords in seconds. Weaknesses: fails if your password isn't on the list.
Think P@ssw0rd beats a dictionary attack? It doesn't. Hacking tools have "Rule Sets" that automatically swap a -> @, s -> $, and o -> 0. To a hacker, Password and P@$$w0rd are effectively the same word.
The Hybrid Attack (The Real Danger)
Modern tools combine both methods. They start with a Dictionary Attack ("smart guessing"). If that fails, they append brute-force suffixes.
- Try:
Summer(Dictionary) - Try:
Summer+1(Hybrid) - Try:
Summer+123(Hybrid) - Try:
Summer+2024(Hybrid)
This catches the vast majority of corporate passwords like CompanyName2024!.
How to Defeat Both Strategies
The defense strategy is simple: Be Long and Random.
- Beat the Dictionary: Use words that aren't related (Passphrase) or use total gibberish (Password Manager). The phrase
correct-horse-battery-stapleisn't in a dictionary because "correcthorsebatterystaple" isn't a word. - Beat Brute Force: Make it long. A 15-character password is mathematically too expensive to brute force.
Quick Tips
- Avoid common patterns: Don't use seasons ("Summer"), months ("July"), or years ("2025").
- Don't reuse passwords: If your password leaks in one breach, it gets added to the "Dictionary" for everyone else.
- Use a Generator: Let a computer pick your password. Humans are incapable of being truly random.
Conclusion
If your password is a single word found in the dictionary (even with a number at the end), you are vulnerable to a dictionary attack. It takes seconds to crack.
If your password is short (under 8 chars), you are vulnerable to brute force. It takes minutes to crack.
The sweet spot? 12+ characters that don't form a predictable sentence. That puts you out of reach of both the smart hacker and the dumb one.
DynamicPassGen Security Team
Security Research & Education
Our security team stays current with the latest password standards, authentication methods, and cybersecurity best practices to provide accurate, actionable guidance for users and organizations. We analyze emerging threats, study real-world breaches, and translate complex security concepts into practical advice you can implement immediately.
